
How to Beat Sneaker Bots with Netacea
- Netacea, Agentless Bot Management
3 minutes read
In part four of our sneaker bot series, we explore a real-world example of how we’ve spotted these badly-behaved bot-teenagers, and what we’ve done to put them on the naughty step.
In earlier parts of this series, we’ve discussed just why the sneaker bot operators are so motivated, and also some of the strategies that you can employ to attempt to stop them. In this edition, we’ll run through a couple of examples of behaviour we’ve identified and then mitigated for one of our bot management customers.
Customer Profile
A major luxury department store with a strong online presence:
- £700m annual turnover
- Four UK stores; global online presence
Client Challenge: Identifying Previously Unknown Attack Vectors
Our customer wasn’t actually aware they had a problem with retail sneaker bots. We had engaged with them for entirely different reasons; however, once our algorithms got to work it quickly became apparent that there was more than one threat to their site.
Solution: Extending Mitigation Strategies to Include Sneaker Bots
In related blogs, we spoke a little bit about how we measureintent, as well as behaviour itself. It’s this combination that allows us to start monitoring the activities of certain undesirables.
For most retail sneaker bots, the behaviour is fairly easy to spot – rarely are they subtle in their actions. The same was true with this particular customer, and we were able to quickly identify and then protect against them. The sneaker bots followed the standard modus operandi: to first monitor the site for a specific shoe (or designer bag, shirt or indeed anything else that has been deemed the sine qua non on any given day – sneaker bots don’t confine themselves to sneakers!).
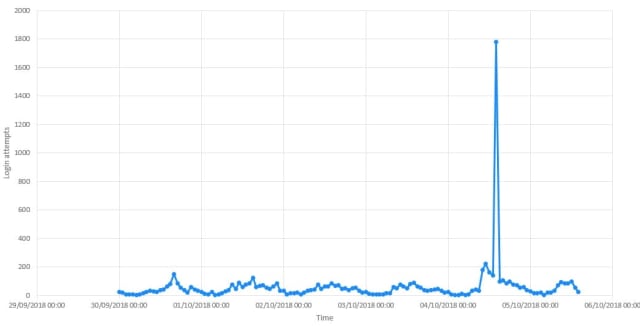
Once the path became live, they sprang into action. The below plot shows the initial monitoring stage, and then the immediate ramp-up to BUY BUY BUY (or at least, attempt to BUY BUY BUY – we were blocking them at this stage):
Intent is Everything
The intent in cases like this is also fairly easy to understand. In this instance, the requests were almost exclusively referencing the Yeezy Triple Black, but in all cases, the bot will have been pre-programmed to look for a specific product. This sort of thing is what sets the traffic apart from that of a normal shopper eager for the latest pair of kicks.
The trick is being able to configure your bot management tool to look for the right red flags and to then take appropriate defensive action. In our case, we’ve found that our custom advanced mitigations including Captcha, showing alternate content, adding challenges to the user journey or cancelling orders, pretty much cover all the bases.
It’s a team sport
One final thing: Netacea employ a team of data scientists, analysts and bot ops staff to protect our customers against this sort of thing. From writing the initial algorithms to tuning them to our customers’ specific sites, to liaising over appropriate action to take – all of this is done in a collaborative fashion. No two customers are the same, and we understand that and want to work with you to ensure that your site is available to REAL team players, and not just the cyber-bullies.
To find out more about how we can help your team beat the bots, contact our team of data scientists today for a consultation.
Subscribe and stay updated
Insightful articles, data-driven research, and more cyber security focussed content to your inbox every week.
By registering, you confirm that you agree to Netacea's privacy policy.
